Spybot Search & Destroy 2.9 Crack + License Key

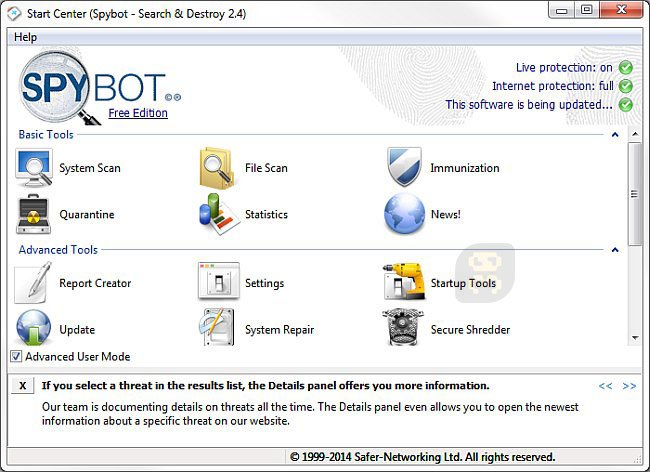
Spybot Search and Destroy 2.9.85.5 Crack is an application for searching for all types of strong malware or threats from hidden files or folders and not only sometimes some users install the software on their PCs secretly without the user’s knowledge and then link such types of software with their device. Then this app can search for such types of software from the computer or mobile and can also eliminate such types of connections and maintain your device privacy or save you from threats. If any malware tries to attack your folders, this app can block access to such types of malware.
Spybot Search & Destroy key can be excellent computer software used to protect against malware and spyware. Furthermore, the security module with this program happens to have a powerful scanner to automatically target the correct malware. Therefore, this program protects a person’s body from files in the form of applications, copied data files, and folders. Also, when you scan your data randomly or manually, it shows the result on the screen. Also, it depends on the user what kind of operation he wants to perform on the scan results.
Spybot Search & Destroy Keygen
Search & Destroy 2.9.85.5 Crack is an experimental, practical, and dependable application that identifies the infected location and cleans the harmful files quickly. Even if you no longer see the signs and symptoms, your system can be infected. The Basic and Advanced sections of Spybot Search & Destroy Crack are free, but the professional section of Spybot Search and Destroy Key is not free. You can use this professional section for free by downloading the full crack version from here. The professional section consists of many powerful features that can protect your device perpetually. In a nutshell, Spybot Search & Destroy Key Latest Version plays a vital role in security and protection.
SpyBot Search & Destroy Key Apart from that, if you scan your data randomly or manually, it shows the effect on the screen. And it is up to the user what kind of performance he wants to perform on the scan result. Also, it allows the user to quickly use the scanning feature which helps the user to increase the speed of the system. Also, if you have any difficulties due to the scanning process, you can get help directly on the Internet. Therefore, it is not yet necessary to scan the entire system to easily scan each set of files. Therefore, the user can see the status of the feature in a separate window to take full advantage of it. In other words, anyone can use it on any type of computer system because it requires less time and space for the user.
Key Features:
- SpyBot Search & Destroy Unlocked Torrent whereas it seemed to incorporate the very
- well and honors pro-government, everything now combines the following and perhaps the most comprehensive cyber security.
- With both the interface that allows people to phone, you have quite a several Pantages.
- There seems to be a dwelling to inhabit and a scan to document every one of the ongoing activities.
- Besides that, the implementation deactivates the surveillance of baked goods and several antivirus news items.
- Block a multitude of components that might be over one another and the.
- When something concerns herpes simplex and other varieties,
- The preceding is the sequence-dependent setup tools that must be eliminated.
- Eliminate the additional responsibilities from your installation as well as installation sectors.
- Because of its many safeguards, this implementation does indeed have a variety of components.
- Consumers always include a strong set regarding the usefulness of this curriculum in more circumstances.
- It educates the customer on how to appropriately use every one of its features and functionalities in some kind of a brief period.
- We can encrypt our confidential knowledge with the help of this technology.
- This database’s real advantage has been that it informs the completion of the
- procedure you’re undertaking on the given database.
- It enables the customers to stop immediately the screening process.
The process. - Something factor to bear in mind though is that it responds to the consumer.
- As a corollary,
- Thousands of citizens have been using this application everywhere worldwide.
What’s New?
- Implemented /silent
- Office 15 (2013) and 16 (2016) Telemetry immunization (Group Policies & Scheduled Tasks)
- Hosts file block default IP and changed from 127.0.0.1 to 0.0.0.0
- Policy for hosts file read-only flag
- Added Own group policy for hosts file blocked IP
- Also, added Group policies for hiding each immunizer
- SSL libraries to the installer
- OpenSSL credits to About Dialogue
- Own scheduled tasks also.
Pros:
- It is used to help and easily get commands from line parameters.
- Therefore, you can get the shredder and record
- Also, used to make BootCD and creation
- While it makes points it gets interesting
Cons:
- It gets a frightful treat from rootkits
System Requirements:
Operating System: all windows
RAM: At least 512 MB
Hard Disk Space: At least 30 MB
Processor: intel core processor at least
Premium Key: LAMQPY-RYGFN-TYUVBE-YRGFHJD VBNEYE-YGNUTT-HGJRIV-RGHIRR WERYF-RSYFH-SRYHFV-SRHDVBDD ARSGFV-SRYFHV-SRYHF-SRYHFDD
How To Crack?
- How To Crack Spybot Search and Destroy
- Extract the zip file using WinRAR or WinZip
- The zip file Installs the Program As Normal.
- After Install Don’t Run the Software.
- Please Always Read the Readme
- Please, Copy and paste the Crack File into the c/program files.
- After Install Run the Software.
- Now Enjoy the Full version.